Our Stats
New Era Technology
New Era has an extensive team of Engineers, Designers, Installers, Technicians, and Sales Professionals, all of whom provide hands-on collaborative consultation backed by deep industry training and certification. From concept and implementation, to training and service, we work in partnership with our clients to meet their goals.
More than 20,000 customers
80+ Offices Worldwide
4,500+ Employees
Explore
Our Services
CloudBlu
Reduce costs and increase flexibility with cloud deployment models that include private cloud services, public cloud services and hybrid solutions.
Professional Services
Gain a team of dedicated consultants and integrators to help implement new technologies, business applications and policies. Maximize your existing assets and bridge business gaps.
Managed Services
Streamline operations and save IT budget with managed IT and AV services with solutions, including staffing, that can be customized to meet the needs of your organization.

SecureBlu
Improve your security posture and minimize risk with a full range of advisory and managed security services. Take advantage of a cutting-edge XDR platform for advanced detection and response capabilities.
Explore
Our Solutions
Collaboration & UC
Work better in-person and across distances with best-in-class collaboration and unified communications solutions. Inspire visitors with AV solutions that create completely immersive experiences.
Data Networking
Connect people, information, and locations with a reliable network infrastructure that meets your business needs and enforces your business policies.
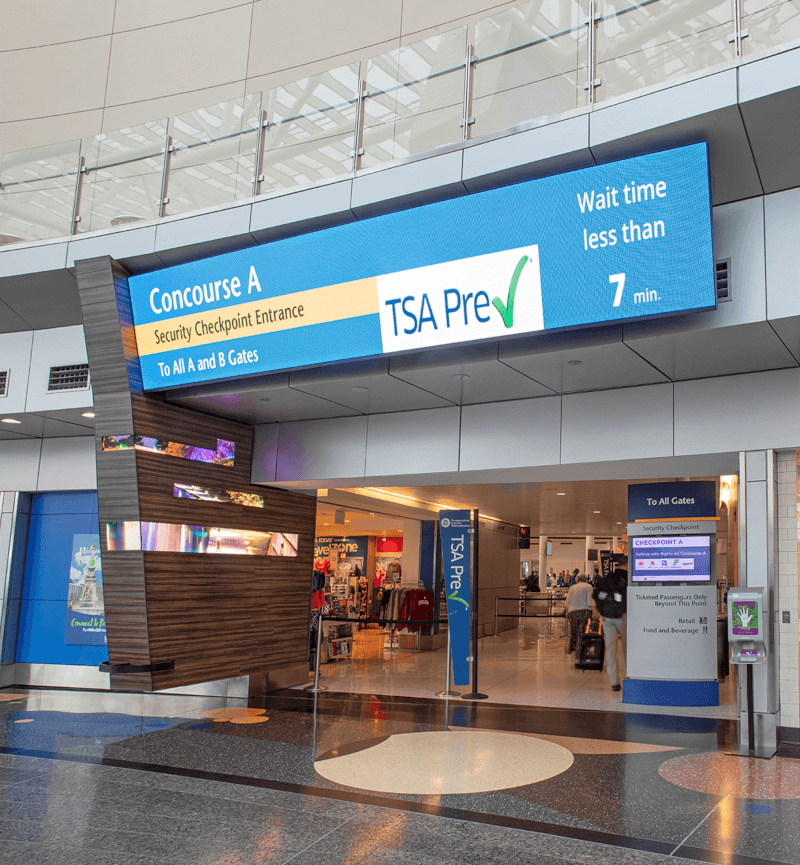
Security & Life Safety
Monitor and control user access to your campus, and ensure the safety of your visitors inside and outside of your facility with comprehensive security and life safety strategies.
Digital Transformation
Digital transformation uses technology to reimagine how businesses work—from strategy to operations to customer connections. New Era delivers holistic digital transformation solutions that position your business for whatever comes next.
Industries
Products That Deliver Real Results for Real Market Needs
Leveraging our extensive knowledge from working with customers across a diverse set of markets, we develop creative, custom solutions designed for your specific industry.
Resources
Our Work
We work with our customers as a trusted technology adviser to deliver valuable solutions that improve efficiencies and experiences.
Blog
Hear directly from our experts to learn more about New Era’s solutions and leading trends in the industry.
Document Library
New Era provides solutions that help more than 20,000 customers worldwide. Navigate through our case studies, solution briefs and white papers to learn more.

 Canada
Canada Australia
Australia New Zealand
New Zealand UAE
UAE United Kingdom
United Kingdom